A recent security issue has been revealed that may affect countless android users, particularly those utilizing cryptocurrency wallet applications. This vulnerability, if left unaddressed, could expose vital private information and funds to malicious actors.
The Cybersecurity Research Team disclosed details about this vulnerability, first identified earlier this year. This issue exists within a common software framework known as [Framework Name], which is embedded in numerous Android apps.

Due to the widespread adoption of this framework, a single compromised application could potentially trigger a cascade of security breaches, affecting a broad spectrum of users.
Understanding the Threat
This type of security breach is categorized as “message redirection.” An attacker sends a specifically crafted message to any application utilizing the vulnerable framework. As a result, the targeted application can be manipulated into releasing sensitive data like authentication keys and account numbers.
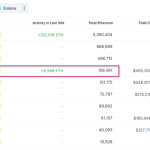
This breach circumvents Android’s security measures, which usually prevent applications from accessing each other’s data. According to recent findings, millions of applications could be at risk, with a significant number being cryptocurrency wallets.
Users fell victim to this vulnerability without needing to engage in risky behavior. Simply by having potentially vulnerable apps installed, they inadvertently exposed their data.

How Companies are Responding
In light of this discovery, rapid action was taken. Collaboration was established between tech giants and security teams to address the vulnerability. A patch was made available shortly thereafter, updating the affected framework.
Both Microsoft and Google have since provided guidance to users on checking for the latest updates through their security apps. This ensures they can verify the integrity of their applications.

There is also an emphasis on the potential risks associated with downloading applications from non-official sources, as these bypass essential security protocols employed by the official app marketplace.
Steps Users Should Take
If users consistently update their applications, they may be in a safer position. However, those who have not taken action since the vulnerability was disclosed should consider taking more comprehensive measures.
Experts recommend transferring funds to newly created wallets with secure, fresh authentication phrases. Any wallets that have remained unpatched during the time of exposure must be treated with caution.
This incident parallels additional security concerns that have surfaced recently regarding mobile device software and has highlighted the urgent need for enhanced security protocols in the cryptocurrency arena.
Image source from Cybersecurity Reports, chart from Example Charts